| 08/Nov/2013
|
Shorewall and Multiple Internet Connections |
Shorewall and Multiple Internet Connections
Tom Eastep and Mr Dash Four
Copyright © 2005, 2006, 2007, 2008, 2009, 2010, 2011, 2012 2013 Thomas M. Eastep,, 2013 Mr Dash Four
Permission is granted to copy, distribute and/or modify this document under the terms of the GNU Free Documentation License, Version 1.2 or any later version published by the Free Software Foundation; with no Invariant Sections, with no Front-Cover, and with no Back-Cover Texts. A copy of the license is included in the section entitled “GNU Free Documentation License”.
Warning
This document describes the Multi-ISP facility in Shorewall 4.4.26 and later. If you are running an earlier release, please see the documentation for that release.
Warning
Reading just Shorewall documentation is probably not going to give you enough background to use this material. Shorewall may make iptables easy but the Shorewall team doesn't have the resources to be able to spoon-feed Linux policy routing to you (please remember that the user's manual for a tractor doesn't teach you to grow corn either). You will likely need to refer to the following additional information:
Multiple Internet Connection Support
Shorewall includes limited support for multiple Internet connections. Limitations of this support are as follows:
-
It utilizes static routing configuration. If there is a change in the routing topopogy, Shorewall must be restarted.
-
The routing changes are made and the route cache is purged when Shorewall is started and when Shorewall is restarted (unless you specify the "-n" option to shorewall restart). Ideally, restarting the packet filter should have no effect on routing.
-
For most routing applications, Quagga is a better solution although it requires that your ISPs offer routing protocol support.
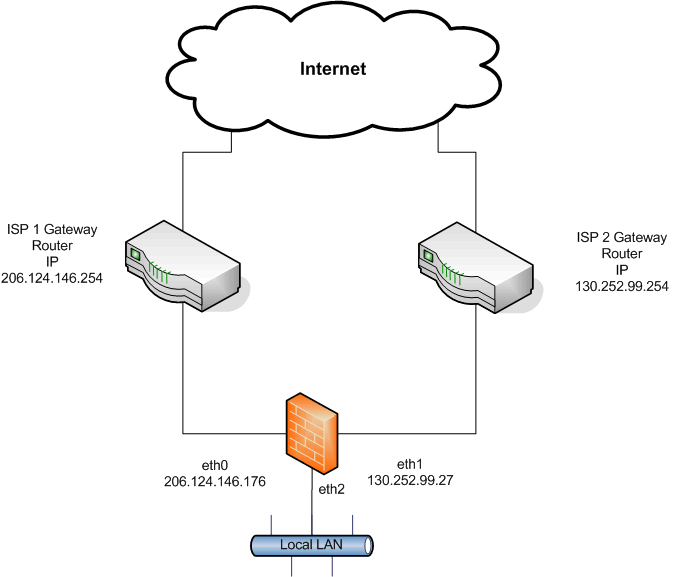
Let's assume that a firewall is connected via two separate Ethernet interfaces to two different ISPs.[1] as in the following diagram.
-
eth0 connects to ISP1. The IP address of eth0 is 206.124.146.176 and the ISP's gateway router has IP address 206.124.146.254.
-
eth1 connects to ISP 2. The IP address of eth1 is 130.252.99.27 and the ISP's gateway router has IP address 130.252.99.254.
-
eth2 connects to the local LAN. Its IP configuration is not relevant to this discussion.
Each of these providers is described in an entry in the file /etc/shorewall/providers.
Entries in /etc/shorewall/providers can specify that outgoing connections are to be load-balanced between the two ISPs. Entries in /etc/shorewall/tcrules and /etc/shorewall/rtrules can be used to direct particular outgoing connections to one ISP or the other. Use of /etc/shorewall/tcrules is not required for /etc/shorewall/providers to work, but in most cases, you must select a unique MARK value for each provider so Shorewall can set up the correct marking rules for you.
When you use the track option in /etc/shorewall/providers, connections from the Internet are automatically routed back out of the correct interface and through the correct ISP gateway. This works whether the connection is handled by the firewall itself or if it is routed or port-forwarded to a system behind the firewall.
Shorewall will set up the routing and will update the /etc/iproute2/rt_tables to include the table names and numbers of the tables that it adds.
Caution
This feature uses packet marking to control the routing. As a consequence, there are some restrictions concerning entries in /etc/shorewall/tcrules:
-
Packet marking for traffic control purposes may not be done in the PREROUTING table for connections involving providers with 'track' specified (see below).
-
You may not use the SAVE or RESTORE options unless you also set HIGH_ROUTE_MARKS=Yes (PROVIDER_OFFSET > 0 with Shorewall 4.4.26 and later) in /etc/shorewall/shorewall.conf.
-
You may not use connection marking unless you also set HIGH_ROUTE_MARKS=Yes (PROVIDER_OFFSET > 0 with Shorewall 4.4.26 and later) in /etc/shorewall/shorewall.conf.
The /etc/shorewall/providers file can also be used in other routing scenarios. See the Squid documentation for an example.
/etc/shorewall/providers File
Entries in this file have the following columns. As in all Shorewall configuration files, enter "-" in a column if you don't want to enter any value.
- NAME
-
The provider name. Must begin with a letter and consist of letters and digits. The provider name becomes the name of the generated routing table for this provider.
- NUMBER
-
A number between 1 and 252. This becomes the routing table number for the generated table for this provider.
- MARK
-
A mark value used in your /etc/shorewall/tcrules file to direct packets to this provider. Shorewall will also mark connections that have seen input from this provider with this value and will restore the packet mark in the PREROUTING CHAIN. Mark values must be in the range 1-255.
Alternatively, you may set HIGH_ROUTE_MARKS=Yes (PROVIDER_OFFSET > 0 with Shorewall 4.4.26 and later) in /etc/shorewall/shorewall.conf. This allows you to:
-
Use connection marks for traffic shaping, provided that you assign those marks in the FORWARD chain.
-
Use mark values > 255 for provider marks in this column.
-
With HIGH_ROUTE_MARKS=Yes (PROVIDER_OFFSET=8), these mark values must be a multiple of 256 in the range 256-65280 (hex equivalent 0x100 - 0xFF00 with the low-order 8 bits being zero); or
-
Set WIDE_TC_MARKS=Yes in shorewall.conf (5) (PROVIDER_OFFSET=16), and use mark values in the range 0x10000 - 0xFF0000 with the low-order 16 bits being zero.
This column may be omitted if you don´t use packet marking to direct connections to a particular provider.
- DUPLICATE
-
Gives the name or number of a routing table to duplicate. May be 'main' or the name or number of a previously declared provider. This field should be be specified as '-' when USE_DEFAULT_RT=Yes in shorewall.conf. When USE_DEFAULT_RT=No (not recommended), this column is normally specified as main.
- INTERFACE
-
The name of the interface to the provider. Where multiple providers share the same interface, you must follow the name of the interface by a colon (":") and the IP address assigned by this provider (e.g., eth0:206.124.146.176). See below for additional considerations.
The interface must have been previously defined in shorewall-interfaces (5). In general, that interface should not have the proxyarp option specified unless loose is given in the OPTIONS column of this entry.
- GATEWAY
-
The IP address of the provider's Gateway router.
You can enter detect here and Shorewall will attempt to automatically determine the gateway IP address.
Hint: "detect" is appropriate for use in cases where the interface named in the INTERFACE column is dynamically configured via DHCP etc. Be sure, however, that you don't have stale dhcp client state files in /var/lib/dhcpcd or /var/lib/dhclient-*.lease because Shorewall may try to use those stale files to determine the gateway address.
The GATEWAY may be omitted (enter '-') for point-to-point links.
- OPTIONS
-
A comma-separated list from the following:
- track
-
Important
Beginning with Shorwall 4.3.3, track defaults to the setting of the TRACK_PROVIDERS option in shorewall.conf (5). To disable this option when you have specified TRACK_PROVIDERS=Yes, you must specify notrack (see below).
If specified, connections FROM this interface are to be tracked so that responses may be routed back out this same interface.
You want to specify 'track' if Internet hosts will be connecting to local servers through this provider. Any time that you specify 'track', you will normally want to also specify 'balance' (see below). 'track' will also ensure that outgoing connections remain stay anchored to a single provider and don't try to switch providers when route cache entries expire.
Use of this feature requires that your kernel and iptables include CONNMARK target and connmark match support (Warning: Until recently, standard Debian™ and Ubuntu™ kernels lacked that support. Both Lenny and Jaunty do have the proper support).
Important
If you are running a version of Shorewall earlier than 4.4.3 and are using /etc/shorewall/providers because you have multiple Internet connections, we recommend that you specify track even if you don't need it. It helps maintain long-term connections in which there are significant periods with no traffic.
- balance
-
The providers that have balance specified will get outbound traffic load-balanced among them. Balancing will not be perfect, as it is route based, and routes are cached. This means that routes to often-used sites will always be over the same provider.
By default, each provider is given the same weight (1) . You can change the weight of a given provider by following balance with "=" and the desired weight (e.g., balance=2). The weights reflect the relative bandwidth of the providers connections and should be small numbers since the kernel actually creates additional default routes for each weight increment.
Important
If you are using /etc/shorewall/providers because you have multiple Internet connections, we recommend that you specify balance even if you don't need it. You can still use entries in /etc/shorewall/tcrules and /etc/shorewall/rtrules to force all traffic to one provider or another.
Note
If you don't heed this advice then please read and follow the advice in FAQ 57 and FAQ 58.
- loose
-
Do not generate routing rules that force traffic whose source IP is an address of the INTERFACE to be routed to this provider. Useful for defining providers that are to be used only when the appropriate packet mark is applied.
Shorewall makes no attempt to consolidate the routing rules added when loose is not specified. So, if you have multiple IP addresses on a provider interface, you may be able to replace the rules that Shorewall generates with one or two rules in /etc/shorewall/rtrules. In that case, you can specify loose to suppress Shorewall's rule generation. See the example below.
- notrack
-
Added in Shorewall 4.4.3. This option turns off the track option.
- optional
-
Note
This option is deprecated in favor of the optional interface option. That option performs the same function.
Shorewall will determine if this interface is up and has a configured IP address. If it is not, a warning is issued and this provider is not configured.
Note
optional is designed to detect interface states that will cause shorewall start or shorewall restart to fail; just because an interface is in a state that Shorewall can [re]start without error doesn't mean that traffic can actually be sent through the interface.
You can supply an 'isusable' extension script to extend Shorewall's interface state detection. See also the Gateway Monitoring and Failover section below.
- src=
source-address -
Specifies the source address to use when routing to this provider and none is known (the local client has bound to the 0 address). May not be specified when an address is given in the INTERFACE column. If this option is not used, Shorewall substitutes the primary IP address on the interface named in the INTERFACE column.
- mtu=
number -
Specifies the MTU when forwarding through this provider. If not given, the MTU of the interface named in the INTERFACE column is assumed.
- fallback[=
weight] -
Indicates that a default route through the provider should be added to the default routing table (table 253). If a weight is given, a balanced route is added with the weight of this provider equal to the specified weight. If the option is given without a weight, a separate default route is added through the provider's gateway; the route has a metric equal to the provider's NUMBER.
Prior to Shorewall 4.4.24, the option is ignored with a warning message if USE_DEFAULT_RT=Yes in shorewall.conf.
Warning
If you set this option on an interface, you must disable route filtering on the interface. Include 'routefilter=0,logmartions=0' in the OPTIONS column of shorewall-interfaces(5).
For those of you who are confused between track and balance:
- COPY
-
A comma-separated list of other interfaces on your firewall. Wildcards specified using an asterisk ("*") are permitted (e.g., tun* ). Usually used only when DUPLICATE is main. Only copy routes through INTERFACE and through interfaces listed here. If you only wish to copy routes through INTERFACE, enter none in this column.
Note
Beginning with Shorewall 4.4.15, provider routing tables can be augmeted with additional routes through use of the /etc/shorewall/routes file.
What an entry in the Providers File Does
Adding another entry in the providers file simply creates an alternate routing table for you (see the LARTC Howto). The table will usually contain two routes:
-
A host route to the specified GATEWAY through the specified INTERFACE.
-
A default route through the GATEWAY.
Note that the first route is omitted if "-" is specified as the GATEWAY; in that case, the default route does not specify a gateway (point-to-point link).
If the DUPLICATE column is non-empty, then routes from the table named in that column are copied into the new table. By default, all routes (except default routes) are copied. The set of routes copied can be restricted using the COPY column which lists the interfaces whose routes you want copied. You will generally want to include all local interfaces in this list. You should exclude the loopback interface (lo) and any interfaces that do not have an IP configuration. You should also omit interfaces like tun interfaces that are created dynamically. Traffic to networks handled by those interfaces should be routed through the main table using entries in /etc/shorewall/rtrules (see Example 2 below) or by using USE_DEFAULT_RT=Yes.
In addition:
-
Unless loose is specified, an ip rule is generated for each IP address on the INTERFACE that routes traffic from that address through the associated routing table.
-
If you specify track, then connections which have had at least one packet arrive on the interface listed in the INTERFACE column have their connection mark set to the value in the MARK column. In the PREROUTING chain, packets with a connection mark have their packet mark set to the value of the associated connection mark; packets marked in this way bypass any prerouting rules that you create in /etc/shorewall/tcrules. This ensures that packets associated with connections from outside are always routed out of the correct interface.
-
If you specify balance, then Shorewall will replace the 'default' route with weight 100 in the 'main' routing table with a load-balancing route among those gateways where balance was specified. So if you configure default routes, be sure that their weight is less than 100 or the route added by Shorewall will not be used.
That's all that these entries do. You still have to follow the principle stated in the Shorewall Routing documentation:
-
Routing determines where packets are to be sent.
-
Once routing determines where the packet is to go, the firewall (Shorewall) determines if the packet is allowed to go there and controls rewriting of the SOURCE IP address (SNAT/MASQUERADE).
The bottom line is that if you want traffic to go out through a particular provider then you must mark that traffic with the provider's MARK value in /etc/shorewall/tcrules and you must do that marking in the PREROUTING chain; or, you must provide the appropriate rules in /etc/shorewall/rtrules.
What an entry in the Providers File Does Not Do
Shorewall itself provides no mechanism for dealing with provider links that are in the up state but not responsive. If you want transparent failover when a link is unresponsive, you must configure all provider interfaces as optional (shorewall-interfaces(5)) then install and configure LSM.
Shorewall-init provides for handling links that go hard down and are later brought back up.
./etc/shorewall/masq and Multi-ISP
If you masquerade a local network, you will need to add masquerade rules for both external interfaces. Referring to the diagram above, if each of the interfaces has only a single IP address and you have no systems with public IP addresses behind your firewall, then I suggest the following simple entries:
#INTERFACE SOURCE ADDRESS
eth0 0.0.0.0/0 206.124.146.176
eth1 0.0.0.0/0 130.252.99.27
If you have a public subnet (for example 206.124.146.176/30) behind your firewall, then use exclusion:
#INTERFACE SOURCE ADDRESS
eth0 !206.124.146.176/29 206.124.146.176
eth1 0.0.0.0/0 130.252.99.27
Note that exclusion is only used on the interface corresponding to internal subnetwork.
If you have multiple IP addresses on one of your interfaces, you can use a similar technique -- simplY exclude the smallest network that contains all of those addresses from being masqueraded.
Warning
Entries in /etc/shorewall/masq have no effect on which ISP a particular connection will be sent through. That is rather the purpose of entries in /etc/shorewall/tcrules and /etc/shorewall/rtrules.
One problem that often arises with Multi-ISP configuration is 'Martians'. If your Internet interfaces are configured with the routefilter option in /etc/shorewall/interfaces (remember that if you set that option, you should also select logmartians), then things may not work correctly and you will see messages like this:
Feb 9 17:23:45 gw.ilinx kernel: martian source 206.124.146.176 from 64.86.88.116, on dev eth1
Feb 9 17:23:45 gw.ilinx kernel: ll header: 00:a0:24:2a:1f:72:00:13:5f:07:97:05:08:00
The above message is somewhat awkwardly phrased. The source IP in this incoming packet was 64.86.88.116 and the destination IP address was 206.124.146.176. Another gotcha is that the incoming packet has already had the destination IP address changed for DNAT or because the original outgoing connection was altered by an entry in /etc/shorewall/masq (SNAT or Masquerade). So the destination IP address (206.124.146.176) may not have been the destination IP address in the packet as it was initially received.
There a couple of common causes for these problems:
-
You have connected both of your external interfaces to the same hub/switch. Connecting multiple firewall interfaces to a common hub or switch is always a bad idea that will result in hard-to-diagnose problems.
-
You are specifying both the loose and balance options on your provider(s). This can cause individual connections to ping-pong back and forth between the interfaces which is almost guaranteed to cause problems.
-
You are redirecting traffic from the firewall system out of one interface or the other using packet marking in your /etc/shorewall/tcrules file. A better approach is to configure the application to use the appropriate local IP address (the IP address of the interface that you want the application to use). See below.
If all else fails, remove the routefilter option from your external interfaces. If you do this, you may wish to add rules to log and drop packets from the Internet that have source addresses in your local networks. For example, if the local LAN in the above diagram is 192.168.1.0/24, then you would add this rule:
#ACTION SOURCE DEST
DROP:info net:192.168.1.0/24 all
Be sure the above rule is added before any other rules with net in the SOURCE column.
This section describes the legacy method of configuring multiple uplinks. It is deprecated in favor of the USE_DEFAULT_RT=Yes configuration described below.
The configuration in the figure at the top of this section would be specified in /etc/shorewall/providers as follows.
#NAME NUMBER MARK DUPLICATE INTERFACE GATEWAY OPTIONS COPY
ISP1 1 1 main eth0 206.124.146.254 track,balance eth2
ISP2 2 2 main eth1 130.252.99.254 track,balance eth2
Other configuration files go something like this:
/etc/shorewall/interfaces:
#ZONE INTERFACE BROADCAST OPTIONS
net eth0 detect …
net eth1 detect …
/etc/shorewall/policy:
#SOURCE DESTINATION POLICY LIMIT:BURST
net net DROP
/etc/shorewall/masq:
#INTERFACE SOURCE ADDRESS
eth0 0.0.0.0/0 206.124.146.176
eth1 0.0.0.0/0 130.252.99.27
Routing a Particular Application Through a Specific Interface
This continues the example in the preceding section.
Now suppose that you want to route all outgoing SMTP traffic from your local network through ISP 2. You would make this entry in /etc/shorewall/tcrules (and if you are running a version of Shorewall earlier than 3.0.0, you would set TC_ENABLED=Yes in /etc/shorewall/shorewall.conf).
#MARK SOURCE DEST PROTO PORT(S) CLIENT USER TEST
# PORT(S)
2:P <local network> 0.0.0.0/0 tcp 25
Note that traffic from the firewall itself must be handled in a different rule:
#MARK SOURCE DEST PROTO PORT(S) CLIENT USER TEST
# PORT(S)
2 $FW 0.0.0.0/0 tcp 25
Shorewall provides considerable flexibility for port forwarding in a multi-ISP environment.
Normal port forwarding rules such as the following will forward from both providers.
/etc/shorewall/rules:
#ACTION SOURCE DEST PROTO DEST PORT(S) SOURCE ORIGINAL
# PORTS(S) DEST
DNAT net loc:192.168.1.3 tcp 25
Continuing the above example, to forward only connection requests from ISP 1, you can either:
-
Qualify the SOURCE by ISP 1's interface:
#ACTION SOURCE DEST PROTO DEST PORT(S) SOURCE ORIGINAL
# PORTS(S) DEST
DNAT net:eth0 loc:192.168.1.3 tcp 25
or
-
Specify the IP address of ISP 1 in the ORIGINAL DEST column:
#ACTION SOURCE DEST PROTO DEST PORT(S) SOURCE ORIGINAL
# PORTS(S) DEST
DNAT net loc:192.168.1.3 tcp 25 - 206.124.146.176
When there are more than two providers, you need to extend the two-provider case in the expected way:
-
For each external address, you need an entry in /etc/shorewall/masq to handle the case where a connection using that address as the SOURCE is sent out of the interfaces other than the one that the address is configured on.
-
For each external interface, you need to add an entry to /etc/shorewall/masq.
If we extend the above example to add eth3 with IP address 16.105.78.4 with gateway 16.105.78.254, then:
/etc/shorewall/providers:
#NAME NUMBER MARK DUPLICATE INTERFACE GATEWAY OPTIONS COPY
ISP1 1 1 main eth0 206.124.146.254 track,balance eth2
ISP2 2 2 main eth1 130.252.99.254 track,balance eth2
ISP3 3 3 main eth3 16.105.78.254 track,balance eth2
/etc/shorewall/masq:
#INTERFACE SUBNET ADDRESS
eth0 0.0.0.0/0 206.124.146.176
eth1 0.0.0.0/0 130.252.99.27
eth3 0.0.0.0/0 16.105.78.4
Applications running on the Firewall -making them use a particular provider
As noted above, separate entries in /etc/shorewall/tcrules are required for traffic originating from the firewall.
Experience has shown that in some cases, problems occur with applications running on the firewall itself. This is especially true when you have specified routefilter on your external interfaces in /etc/shorewall/interfaces (see above). When this happens, it is suggested that you have the application use specific local IP addresses rather than 0.
Examples:
-
Squid: In squid.conf, set tcp_outgoing_address to the IP address of the interface that you want Squid to use.
-
In OpenVPN, set local (--local on the command line) to the IP address that you want the server to receive connections on.
Note that some traffic originating on the firewall doesn't have a SOURCE IP address before routing. At least one Shorewall user reports that an entry in /etc/shorewall/rtrules with 'lo' in the SOURCE column seems to be the most reliable way to direct such traffic to a particular ISP.
Example:
#SOURCE DEST PROVIDER PRIORITY
lo - shorewall 1000
/etc/shorewall/rtrules (formerly /etc/shorewall/route_rules)
The rtrules file allows assigning certain traffic to a particular provider just as entries in the tcrules file. The difference between the two files is that entries in rtrules are independent of Netfilter.
Routing rules are maintained by the Linux kernel and can be displayed using the ip rule ls command. When routing a packet, the rules are processed in turn until the packet is successfully routed.
gateway:~ # ip rule ls
0: from all lookup local <=== Local (to the firewall) IP addresses
10001: from all fwmark 0x1 lookup Blarg <=== This and the next rule are generated by the
10002: from all fwmark 0x2 lookup Comcast 'MARK' values in /etc/shorewall/providers.
20000: from 206.124.146.176 lookup Blarg <=== This and the next rule are generated unless
20256: from 24.12.22.33 lookup Comcast 'loose' is specified; based in the output of 'ip addr ls'
32766: from all lookup main <=== This is the routing table shown by 'iproute -n'
32767: from all lookup default <=== This table is usually empty
gateway:~ #
In the above example, there are two providers: Blarg and Comcast with MARK 1 going to Blarg and mark 2 going to Comcast.
Columns in the rtrules file
Columns in the file are:
- SOURCE (Optional)
-
An ip address (network or host) that matches the source IP address in a packet. May also be specified as an interface name optionally followed by ":" and an address. If the device 'lo' is specified, the packet must originate from the firewall itself.
- DEST (Optional)
-
An ip address (network or host) that matches the destination IP address in a packet.
If you choose to omit either SOURCE or DEST, place "-" in that column. Note that you may not omit both SOURCE and DEST.
- PROVIDER
-
The provider to route the traffic through. May be expressed either as the provider name or the provider number.
- PRIORITY
-
The rule's priority which determines the order in which the rules are processed.
1000-1999 Before Shorewall-generated 'MARK' rules
11000- 11999 After 'MARK' rules but before Shorewall-generated rules for ISP interfaces.
26000-26999 After ISP interface rules but before 'default' rule.
Rules with equal priority are applied in the order in which they appear in the file.
- MARK (Optional - added in Shorewall 4.4.25)
-
Mark and optional mask in the form mark[/mask]. For this rule to be applied to a packet, the packet's mark value must match the mark when logically anded with the mask. If a mask is not supplied, Shorewall supplies a suitable provider mask.
For those VPN types that use routing to direct traffic to remote VPN clients (including but not limited to OpenVPN in routed mode and PPTP), the VPN software adds a host route to the main table for each VPN client. The best approach is to use USE_DEFAULT_RT=Yes as described below. If that isn't possible, you must add a routing rule in the 1000-1999 range to specify the main table for traffic addressed to those clients. See Example 2 below.
If you have an IPSEC gateway on your firewall, be sure to arrange for ESP packets to be routed out of the same interface that you have configured your keying daemon to use.
Example 1: You want all traffic entering the firewall on eth1 to be routed through Comcast.
#SOURCE DEST PROVIDER PRIORITY
eth1 - Comcast 1000
With this entry, the output of ip rule ls would be as follows.
gateway:~ # ip rule ls
0: from all lookup local
1000: from all iif eth1 lookup Comcast
10001: from all fwmark 0x1 lookup Blarg
10002: from all fwmark 0x2 lookup Comcast
20000: from 206.124.146.176 lookup Blarg
20256: from 24.12.22.33 lookup Comcast
32766: from all lookup main
32767: from all lookup default
gateway:~ #
Note that because we used a priority of 1000, the test for eth1 is inserted before the fwmark tests.
Example 2: You use OpenVPN (routed setup w/tunX) in combination with multiple providers. In this case you have to set up a rule to ensure that the OpenVPN traffic is routed back through the tunX interface(s) rather than through any of the providers. 10.8.0.0/24 is the subnet chosen in your OpenVPN configuration (server 10.8.0.0 255.255.255.0).
#SOURCE DEST PROVIDER PRIORITY
- 10.8.0.0/24 main 1000
/etc/shorewall/routes File
Beginning with Shorewall 4.4.15, additional routes can be added to the provider routing tables using the /etc/shorewall/routes file.
The columns in the file are as follows.
- PROVIDER
-
The name or number of a provider defined in shorewall-providers (5).
- DEST
-
Destination host address or network address.
- GATEWAY (Optional)
-
If specified, gives the IP address of the gateway to the DEST.
Beginning with Shorewall 4.5.14, you may specify blackhole in this column to create a blackhole route. When blackhole is specified, the DEVICE column must be empty.
Beginning with Shorewall 4.5.15, you may specify prohibit or unreachable to create a prohibit or unreachable route respectively. Again, the DEVICE column must be empty.
See the next section for additional information.
- DEVICE (Optional)
-
Specifies the device route. If neither DEVICE nor GATEWAY is given, then the INTERFACE specified for the PROVIDER in shorewall-providers (5).
Assume the following entry in /etc/shorewall/providers:
#NAME NUMBER MARK DUPLICATE INTERFACE GATEWAY OPTIONS COPY
Comcast 1 - xxx eth2 ....
The following table gives some example entries in the file and the ip route command which results.
#PROVIDER DEST GATEWAY DEVICE | Generated Command
Comcast 172.20.1.0/24 - eth0 | ip -4 route add 172.20.1.0/24 dev eth0 table 1
Comcast 192.168.4.0/24 172.20.1.1 | ip -4 route add 192.168.1.0/24 via 172.20.1.1 table 1
Comcast 192.168.4.0/24 | ip -4 route add 192.168.4.0/24 dev eth2 table 1
Null routing is a type of routing which discards a given packet instead of directing it through a specific predefined route. Generally speaking, there are 3 different types of Null routing as indicated below:
-
Unreachable routes
When used, a request for a routing decision returns a destination with an unreachable route type, an ICMP unreachable is generated (icmp type 3) and returned to the source address.
Example:
ip route add unreachable 10.22.0.12
ip route add unreachable 192.168.14.0/26
ip route add unreachable 82.32.0.0/12
Unreachable routes are usually indicated by a dash ("-") in the "Iface" column when "route -n" is executed:
~# route -n
Kernel IP routing table
Destination Gateway Genmask Flags Metric Ref Use Iface
10.22.0.12 - 255.255.255.255 !H 0 - 0 -
192.168.14.0 - 255.255.255.192 ! 0 - 0 -
82.32.0.0 - 255.240.0.0 ! 0 - 0 -
-
Prohibit routes
Similar to "unreachable" routes above, when a request for a routing decision returns a destination with a prohibit route type, the kernel generates an ICMP prohibited to return to the source address.
Example:
ip route add prohibit 10.22.0.12
ip route add prohibit 192.168.14.0/26
ip route add prohibit 82.32.0.0/12
"Prohibit" type routes are also indicated by a dash in the "Iface" column as shown above.
-
Blackhole routes
The difference between this type of routing and the previous two listed above is that a packet matching a route with the route type blackhole is simply discarded (DROPed). No ICMP is sent and no packet is forwarded.
Example:
ip route add blackhole 10.22.0.12
ip route add blackhole 192.168.14.0/26
ip route add blackhole 82.32.0.0/12
Blackhole routes are usually indicated with a star ("*") in the "Iface" column:
~# route -n
Kernel IP routing table
Destination Gateway Genmask Flags Metric Ref Use Iface
10.22.0.12 0.0.0.0 255.255.255.255 UH 0 0 0 *
192.168.14.0 0.0.0.0 255.255.255.192 U 0 0 0 *
82.32.0.0 0.0.0.0 255.240.0.0 U 0 0 0 *
Null Routing Implementation in Shorewall
As of Shorewall 4.5.14, the only type of null routing implemented in Shorewall is "blackhole" routing. This can be specified in two different ways as described below.
-
Null Routing with NULL_ROUTE_RFC1918 shorewall.conf configuration option.
When NULL_ROUTE_RFC1918 is set to Yes, it causes Shorewall to null-route the IPv4 address ranges reserved by RFC1918 (private networks).
When combined with route filtering (ROUTE_FILTER=Yes or routefilter in shorewall-interfaces(5)), this option ensures that packets with an RFC1918 source address are only accepted from interfaces having known routes to networks using such addresses.
When this option is used, the blackhole routes for all RFC1918 subnets are defined for the "main" routing table only. These, however, can be copied over to different routing tables or further customised and fine-tuned to suit individual needs by using the "routes" file (see below).
For example, by specifying NULL_ROUTE_RFC1918=Yes in shorewall.conf, Shorewall generates 3 different route statements to be executed at Shorewall startup:
ip route replace blackhole 10.0.0.0/8
ip route replace blackhole 172.16.0.0/12
ip replace blackhole 192.168.0.0/16
Important
When NULL_ROUTE_RFC1918=Yes is used, Shorewall creates a shell script file in ${VARDIR}/undo_rfc1918_routing to undo the null routing, if needed (see below as to some instances when this may be necessary).
-
Null Routing Using Shorewall "routes" (added in Shorewall 4.5.14)
By definition, entries in this file are used to define routes to be added to provider routing tables, including the default routing table (main).
This option allows for a better control over what is defined as a null route in Shorewall and also allows for custom-defined subnets (in addition to RFC1918 type networks) to be added. Blackhole routes defined in this way need to include the word "blackhole" in the GATEWAY column and the DEVICE column must also be ommitted (see example below).
Example of use (/etc/shorewall/routes):
#PROVIDER DEST GATEWAY DEVICE
main 10.0.0.0/8 blackhole
dmz 82.32.0.0/12 blackhole
dmz 192.168.14.0/26 blackhole
The above generates the following 3 statements for execution upon Shorewall startup:
ip route add blackhole 10.0.0.0/8 table main
ip route add blackhole 82.32.0.0/12 table dmz
ip route add blackhole 192.168.14.0/26 table dmz
Important
When blackhole routes are added to a provider (including 'main'), Shorewall creates a shell script file in ${VARDIR}/undo_provider_routing to undo the routing, if needed (see below as to some instances when this may be necessary).
Beginning with Shorewall 4.5.15, Shorewall also supports "unreachable" and "prohibit" routing.
-
The NULL_ROUTE_RFC1918 option may be set to "blackhole", "prohibit" or "unreachable" in addition to "Yes" and "No".
Shorewall will create the three route statements using the specified type type. For compatibility with earlier releases, "Yes" is equivalent to "blackhole".
For example, if NULL_ROUTE_RFC1918=prohibit, then the following three route statements will be executed at Shorewall startup:
ip route replace prohibit 10.0.0.0/8
ip route replace prohibit 172.16.0.0/12
ip replace prohibit 192.168.0.0/16
-
The words "prohibit" and "unreachable" may be placed in the GATEWAY column of /etc/shorewall/routes.
The DEVICE column must be omitted.
Example of use (/etc/shorewall/routes):
#PROVIDER DEST GATEWAY DEVICE
main 10.0.0.0/8 unreachable
dmz 82.32.0.0/12 unreachable
dmz 192.168.14.0/26 unreachable
The above generates the following 3 statements for execution upon Shorewall startup:
ip route add unreachable 10.0.0.0/8 table main
ip route add unreachable 82.32.0.0/12 table dmz
ip route add unreachable 192.168.14.0/26 table dmz
Important
When prohibit or unreachable routes are added to a provider (including 'main'), Shorewall creates a shell script file in ${VARDIR}/undo_provider_routing to undo the routing, if needed (see below as to some instances when this may be necessary).
Important Points To Remember When Using Null Routing in Shorewall
-
In order to create "pinhole" in a particular blackhole route, at least one route needs to be defined in addition to the null route.
Lets take the following example: We need to null-route all addresses from the 10.0.0.0/8 range, except 10.1.0.0/24. In such a case we need to define two routes in our "routes" file (assuming the default "main" routing table is used and also assuming that 10.1.0.0/24 is routed via the default gateway on eth0 and we need to use 'blackhole' type null routing).
/etc/shorewall/routes:
#PROVIDER DEST GATEWAY DEVICE
main 10.0.0.0/8 blackhole
main 10.1.0.0/24 - eth0
The above will generate 2 statements for execution when Shorewall starts:
ip route replace blackhole 10.0.0.0/8 table main
ip route replace 10.1.0.0/24 table main
The order in which the two routes above are defined in "routes" is not important, simply because, by definition, routes with lower mask value are always traversed first. In that way, packets originating from or destined to 10.1.0.0/24 will always be processed before the 10.0.0.0/8 blackhole route.
-
Null routes, by their definition, are not attached to any network device. What this means in reality is that when the status of a particular device changes (either going up or down), that has absolutely no effect on the null routes defined (as already indicated, these are "static" and can only be removed by executing "ip route del" or by executing the relevant ${VARDIR}/undo_*_routing shell script).
Important
The ${VARDIR}/undo_*_routing scripts generated by Shorewall 4.5.14 and earlier cannot be executed directly from the shell without first sourcing ${SHAREDIR}/shorewall/functions. Example:
. /usr/share/shorewall/functions
. /var/lib/shorewall/undo_x_routing
This sometimes may lead to undesirable side effect: when a network interface goes down (even temporarily), then all routes defined or attached to that interface are simply deleted from the routing table by the kernel, while the blackhole routes are untouched.
Lets take our example above: when eth0 goes down, then the route we defined in "routes" for our private subnet (10.1.0.0/24) will be deleted from the routing table. As soon as eth0 goes back up again, unless the route for our private 10.1.0.0/24 subnet is defined again, all packets originating from or destined to 10.1.0.0/24 will simply be dropped by the kernel!
An indication of this type of behaviour is getting endless "martian" packets reported |
|
|
|